TL;DR: Twitter acknowledged a knowledge breach which will have unmasked pseudonymous person accounts. Whereas it did not float any precise numbers, earlier studies indicated a vulnerability uncovered greater than 5.4 million Twitter IDs and related telephone numbers and electronic mail addresses. Twitter patched the safety gap in January, however a “dangerous actor” claims he used it the month earlier than to scrape the info.
Final week, Twitter confirmed that hackers had compromised some accounts on its platform. Builders created the flaw with a June 2021 replace for its Android shopper, that allowed a nasty actor to affiliate person accounts with electronic mail addresses and telephone numbers. Twitter discovered of the vulnerability by means of its bug bounty program in January 2022 and patched it instantly pondering that no person had been affected.
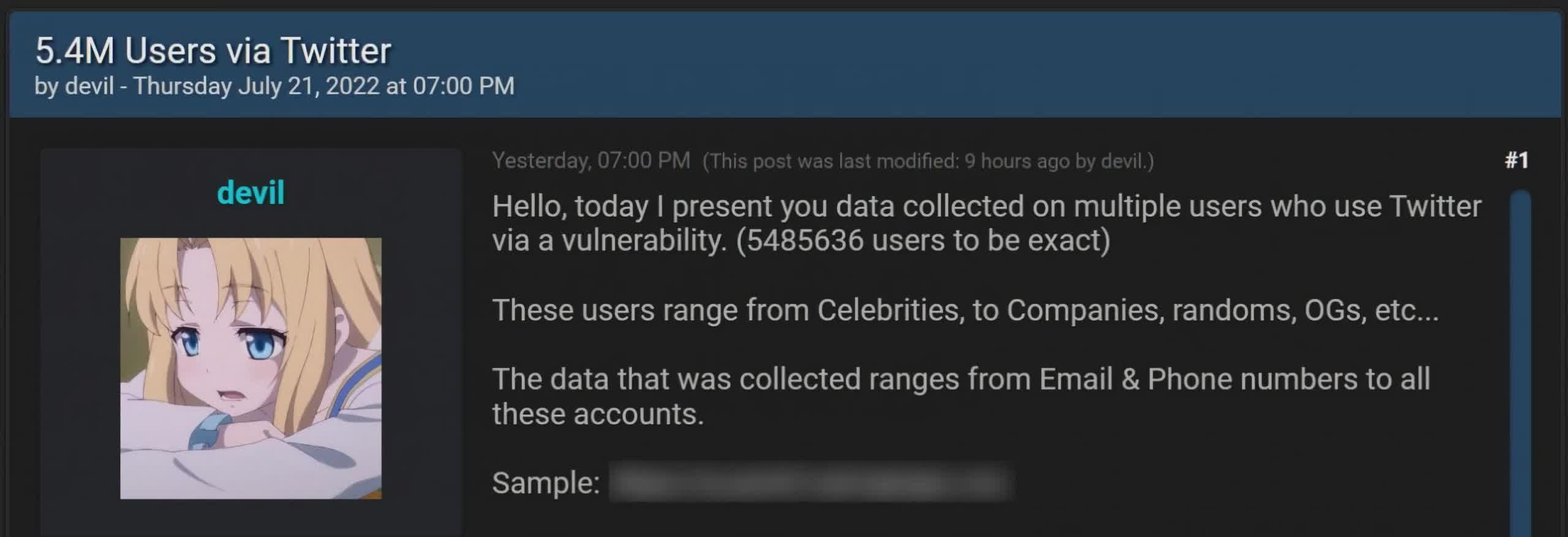
Nevertheless, final month BleepingComputer reported it had discovered a database on a hacker discussion board containing the telephone numbers and electronic mail addresses related to over 5.4 million Twitter accounts.
“Hiya, at this time I current you information collected on a number of customers who use Twitter by way of a vulnerability. (5485636 customers to be actual),” the hacker who calls himself “satan” stated in his put up. “These customers vary from Celebrities, to Corporations, randoms, OGs, and many others [sic].”
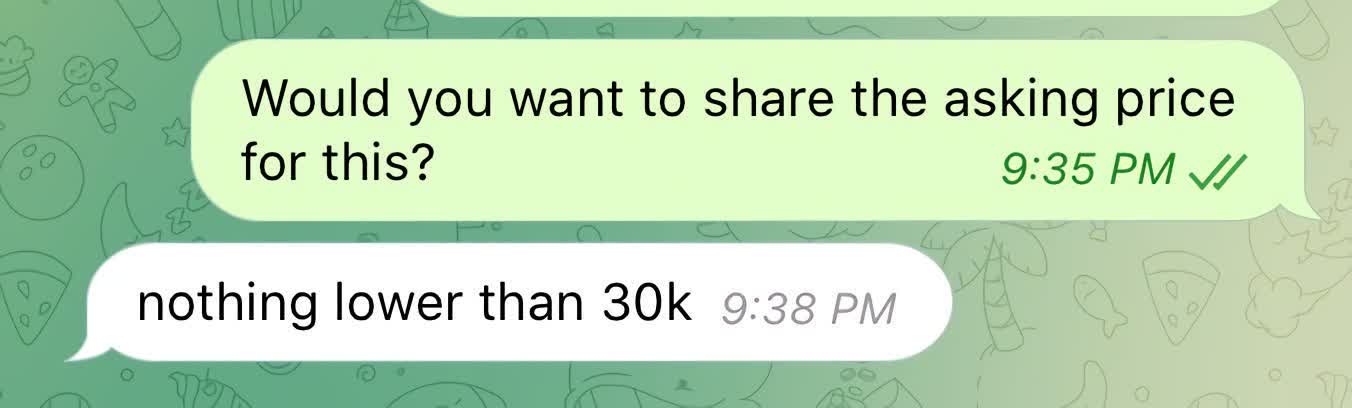
Restore Privateness notes that satan needs to get not less than $30,000 for the stolen information and stated that he’d already had some bites from events.
A safety researcher and bug bounty hunter going by “zhirinovskiy” says the flaw lets anybody receive the Twitter ID of any person by submitting a telephone quantity/electronic mail. The exploit works even when a person’s account is ready to be undiscoverable within the settings. It additionally requires no authentication — only a handful of code.
“The bug exists because of the proccess of authorization used within the Android Consumer of Twitter,” zhirinovskiy stated, who reported the flaw by means of HackerOne. “Particularly within the procces of checking the duplication of a Twitter account [sic].”
Basically, satan would feed the system telephone numbers or emails and it might return whether or not these had been related to Twitter IDs. From there it is a pretty easy matter to create a profile from publicly obtainable posts and different info.
Zhirinovskiy reported the flaw to Twitter on January 1, and builders issued a repair on January 13. Nevertheless, satan claims he collected the info in December 2021 earlier than it was patched. Some have instructed that satan and zhirinovskiy are the identical individual and that he’s attempting to money out on each ends. Satan denies these allegations with virtually an excessive amount of vigor — as if he has one thing to cover.
“I do not wish to white hat in hassle who reported it on H1 [sic],” he instructed BleepingComputer. “I suppose lots of people try to attach him to me, I’d be pissed if I used to be him. So I cant stress this sufficient I’ve nothing to do w him nor H1.”
Twitter’s affirmation doesn’t point out the variety of compromised person accounts, however it’s fairly clear we’re coping with the identical vulnerability that zhirinovskiy reported and satan exploited. The corporate stated that it might notify affected customers, presumably by means of their now uncovered electronic mail tackle. It significantly famous nameless accounts.
“When you function a pseudonymous Twitter account, we perceive the dangers an incident like this may introduce and deeply remorse that this occurred. To maintain your identification as veiled as doable, we advocate not including a publicly identified telephone quantity or electronic mail tackle to your Twitter account.”
Though passwords weren’t compromised, Twitter advises any customers with considerations to make use of two-factor authentication apps or {hardware} safety keys to guard their accounts.
Picture credit score: Discussion board Submit by BleepingComputer, Satan Chat by Restore Privateness



