It’s turning into clearer that scams are going past the e-mail phishing emails we’ve grow to be so accustomed to. Microsoft Groups has grow to be a hotbed of impersonation scams. We’ll be highlighting those that you simply and your staff ought to concentrate on.
What Microsoft Groups impersonation scams ought to I be searching for?
An impersonation assault is a message from a scammer, posing as somebody in what you are promoting. It’s typically somebody in from IT or payroll. They might ask you to click on on a hyperlink, share your display screen or present delicate credentials.
“The Microsoft Groups assist desk impersonation assault works as a result of it weaponises belief,” mentioned Andrea Sivieri, chief product and expertise officer at CoreView . “Organisations are placing themselves in danger as a result of native M365 controls had been constructed for administration, not for resilience towards real-time social engineering.”
He added that, for hackers, all they want is a couple of user-approved clicks they usually have gained entry to Fast Help in addition to the sufferer’s e mail and different accounts. This results in information exfiltration over HTTPS. All of it occurs with out triggering any suspicion.
However as soon as they’re in, the assaults might preserve coming.
“Information theft is simply the opening transfer,” mentioned Sivieri. He mentioned that after attackers have privileged entry by this type of social engineering, the identical foothold opens the door to full tenant ransom situations. Attackers can encrypt OneDrive and SharePoint content material at scale, locking reputable directors out of the tenant by hijacking International Admin accounts and conditional entry insurance policies.
They’ll additionally hijack native M365 options like sensitivity labels, that render information inaccessible, with out ever deploying conventional ransomware. Restoration from a tenant takeover can take weeks and sometimes requires Microsoft to intervene instantly.
“We’ve seen instances the place companies lose entry to important M365 companies for weeks as a result of they should reconfigure their tenants from scratch,” mentioned Rob Edmondson, principal technologist of Microsoft 365, additionally at CoreView. “Microsoft doesn’t present a backup for these configurations. As a result of Microsoft doesn’t alert safety groups when configurations are modified, these assaults could be tough for conventional safety instruments to detect.”
Companies must deal with their Microsoft 365 tenant as important infrastructure, he concludes. This might imply segmenting tenants to cut back the blast radius, detecting when configurations are modified, and conserving a backup of your tenant configurations so you may restore them shortly if attackers change them.
Now, lets get into the specifics of what assaults you would possibly expertise.
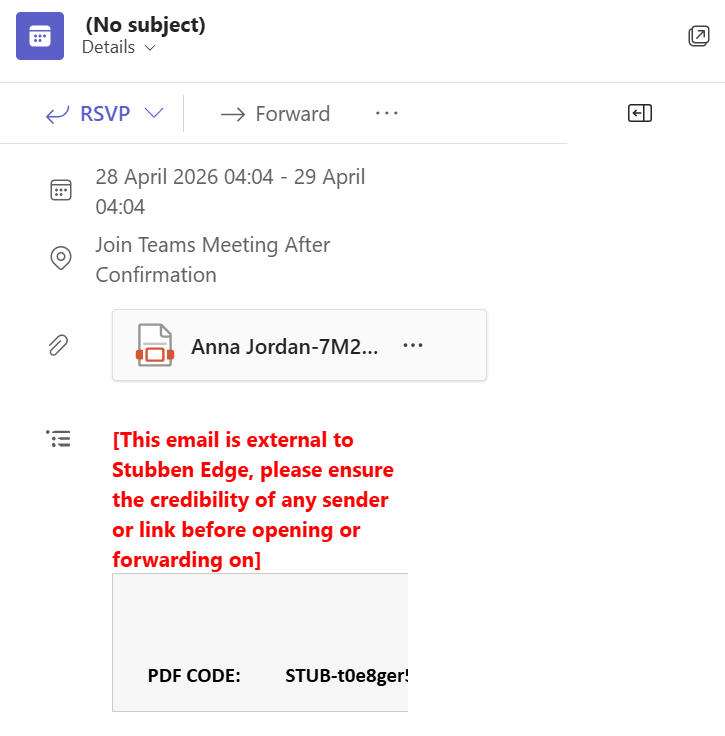
Pressing assembly requests
In these instances, attackers use urgency of their messaging to encourage you to behave shortly. They’ll typically be framed as IT safety alerts or some form of billing challenge. Once more, they’ll normally be from a assist service similar to IT, with a pretend checkmark to try to show authenticity. They might ask you to obtain pretend distant assist instruments like some model of Fast Help which is a fraudulent imitation of the true factor. It is likely to be the case that they direct you to fraudulent web sites or persuade you to obtain recordsdata containing malware.
Groups assembly scams
Once more, scammers on a voice name may very well be impersonating somebody from HR, finance or IT. Nonetheless, when you incessantly work with individuals exterior the enterprise, scammers may very well be impersonating them, too. All of it appears completely reputable, chatting to a long-time contact, till you come throughout an odd request similar to ‘use desktop solely’. That’s actually because scammers’ malicious software program solely runs on PCs.
The scammer will ask you to run some form of script in your command immediate, reassuring you that it’s okay to take action. They’ll strain you with the prospect of letting down shoppers by not having the ability to entry the assembly.
There are pink flags so that you can be on the hunt for. Extra on that in a minute.
QR code
This tactic is named ‘quishing’. A scammer will impersonate a member of your organisation and ship you a QR code, asking you to scan it urgently and full a job. It may very well be one thing like updating your login particulars or verifying your account.
You’ll then be redirected to a phishing website that appear to be a Microsoft verification website. The scammers will seize your data after you’ve logged it and use that to let themselves into your system. From there, they’ll steal information and enact ransomware assaults.
Nefarious hyperlinks in chat
Some impersonators would possibly merely ship you fraudulent hyperlinks in chat or false assembly requests. It really works in a lot the identical method because the scams above, however it’ll simply be the hyperlink with out the frilly set-up. The hyperlink may very well be to one thing like an replace request or account verification.
Be further cautious when you get a random hyperlink or assembly invitation that you simply’re not anticipating, like I did.
How you can forestall Microsoft Groups impersonation assaults
There are many issues that you are able to do to guard what you are promoting that received’t blow your IT finances.
Common
- Look out for indicators of the individual being from exterior your organisation. It’ll normally be marked as [External] or comparable. If doubtful, don’t have interaction with it.
- Be suspicious of imprecise or generic language. Folks in your organization groups will know extra about software program you utilize and different members of your staff, for instance.
- Disable exterior messages. This one works higher for workers who don’t work together with anyone exterior the corporate. Any threat limitation is useful.
- Present coaching to your staff. They’ll be higher in a position to recognise the place they might be focused together with tell-tale indicators of phishing and different scams.
- Allow multi-factor authentication (MFA). Do that so far as you may.
- Make sure that your anti-virus, firewall and different safety features are updated. Basic recommendation, however nonetheless price mentioning. Up to date software program closes up any safety gaps from earlier variations.
- Confirm suspicious messages by a separate channel. Contact IT on e mail, for instance, simply to guarantee that it’s them.
- Ask HR, finance and IT to substantiate actions they’re taking by contacting employees by a separate channel. When you have payroll and IT groups, ask them to substantiate actions they should take by calling or emailing employees members earlier than they achieve this.
- Disable the Fast Help operate. Microsoft’s Fast Help simply permits customers to share their display screen or hand management of their machine over to a different individual. Until it’s enterprise important, eliminate it.
For Microsoft Groups conferences
- By no means run instructions from a gathering web page. You’ll most likely be pressured into appearing shortly to affix the assembly, one other pink flag.
- Pay attention to finishing “powershell -ep bypass” and “iex” instructions. The previous will disable your safety; the latter executes downloaded code with out additional prompts.
- Test for uncommon URLs. Microsoft conferences ought to have groups.microsoft.com or groups.reside.com.
- Don’t be part of conferences which are ‘desktop solely’ or comparable. Scammers need you to affix on the machine that you simply primarily use for work in order that they’ll entry your recordsdata or unfold malware. As talked about, the malicious software program that they use could solely run on desktop.
Learn extra
How you can present cybersecurity coaching to your house staff – Discover out what cybersecurity coaching info to incorporate, tips on how to ship it and what follow-up assets to supply to your house staff



